标签: kubernetes、kubernetes-dashboard
先决条件
一个健康的Kubernetes集群
Nginx-ingress(如果是traefik只要稍微改一下ingress的annotations)
准备所需要的YAML文件
kubernetes-dashboard.yaml
# Copyright 2017 The Kubernetes Authors.## Licensed under the Apache License, Version 2.0 (the "License");# you may not use this file except in compliance with the License.# You may obtain a copy of the License at## http://www.apache.org/licenses/LICENSE-2.0## Unless required by applicable law or agreed to in writing, software# distributed under the License is distributed on an "AS IS" BASIS,# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.# See the License for the specific language governing permissions and# limitations under the License.# ------------------- Dashboard Secret ------------------- #apiVersion: v1kind: Secretmetadata:labels:k8s-app: kubernetes-dashboardname: kubernetes-dashboard-certsnamespace: kube-systemtype: Opaque---# ------------------- Dashboard Service Account ------------------- #apiVersion: v1kind: ServiceAccountmetadata:labels:k8s-app: kubernetes-dashboardname: kubernetes-dashboardnamespace: kube-system---# ------------------- Dashboard Role & Role Binding ------------------- #kind: RoleapiVersion: rbac.authorization.k8s.io/v1metadata:name: kubernetes-dashboard-minimalnamespace: kube-systemrules:# Allow Dashboard to create 'kubernetes-dashboard-key-holder' secret.- apiGroups: [""]resources: ["secrets"]verbs: ["create"]# Allow Dashboard to create 'kubernetes-dashboard-settings' config map.- apiGroups: [""]resources: ["configmaps"]verbs: ["create"]# Allow Dashboard to get, update and delete Dashboard exclusive secrets.- apiGroups: [""]resources: ["secrets"]resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]verbs: ["get", "update", "delete"]# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.- apiGroups: [""]resources: ["configmaps"]resourceNames: ["kubernetes-dashboard-settings"]verbs: ["get", "update"]# Allow Dashboard to get metrics from heapster.- apiGroups: [""]resources: ["services"]resourceNames: ["heapster"]verbs: ["proxy"]- apiGroups: [""]resources: ["services/proxy"]resourceNames: ["heapster", "http:heapster:", "https:heapster:"]verbs: ["get"]---apiVersion: rbac.authorization.k8s.io/v1kind: RoleBindingmetadata:name: kubernetes-dashboard-minimalnamespace: kube-systemroleRef:apiGroup: rbac.authorization.k8s.iokind: Rolename: kubernetes-dashboard-minimalsubjects:- kind: ServiceAccountname: kubernetes-dashboardnamespace: kube-system---# ------------------- Dashboard Deployment ------------------- #kind: DeploymentapiVersion: apps/v1beta2metadata:labels:k8s-app: kubernetes-dashboardname: kubernetes-dashboardnamespace: kube-systemspec:replicas: 1revisionHistoryLimit: 10selector:matchLabels:k8s-app: kubernetes-dashboardtemplate:metadata:labels:k8s-app: kubernetes-dashboardspec:containers:- name: kubernetes-dashboard#image: k8s.gcr.io/kubernetes-dashboard-amd64:v1.8.3#image: mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.10.1image: registry-vpc.cn-hangzhou.aliyuncs.com/xmk8s/kubernetes-dashboard-amd64:v1.10.1ports:- containerPort: 8443protocol: TCPargs:- --auto-generate-certificates- --token-ttl=0# Uncomment the following line to manually specify Kubernetes API server Host# If not specified, Dashboard will attempt to auto discover the API server and connect# to it. Uncomment only if the default does not work.# - --apiserver-host=http://my-address:portvolumeMounts:- name: kubernetes-dashboard-certsmountPath: /certs# Create on-disk volume to store exec logs- mountPath: /tmpname: tmp-volumelivenessProbe:httpGet:scheme: HTTPSpath: /port: 8443initialDelaySeconds: 30timeoutSeconds: 30volumes:- name: kubernetes-dashboard-certssecret:secretName: kubernetes-dashboard-certs- name: tmp-volumeemptyDir: {}serviceAccountName: kubernetes-dashboard# Comment the following tolerations if Dashboard must not be deployed on mastertolerations:- key: node-role.kubernetes.io/mastereffect: NoSchedule---# ------------------- Dashboard Service ------------------- #kind: ServiceapiVersion: v1metadata:labels:k8s-app: kubernetes-dashboardkubernetes.io/cluster-service: "true"addonmanager.kubernetes.io/mode: Reconcilename: kubernetes-dashboardnamespace: kube-systemspec:ports:- port: 443targetPort: 8443selector:k8s-app: kubernetes-dashboardtype: NodePort复制
ui-admin-rbac.yaml
kind: ClusterRoleapiVersion: rbac.authorization.k8s.io/v1metadata:name: ui-adminrules:- apiGroups:- ""resources:- services- services/proxyverbs:- '*'---apiVersion: rbac.authorization.k8s.io/v1kind: RoleBindingmetadata:name: ui-admin-bindingnamespace: kube-systemroleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: ui-adminsubjects:- apiGroup: rbac.authorization.k8s.iokind: Username: admin复制
admin-user-sa-rbac.yaml
apiVersion: v1kind: ServiceAccountmetadata:name: admin-usernamespace: kube-system---apiVersion: rbac.authorization.k8s.io/v1kind: ClusterRoleBindingmetadata:name: admin-userroleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: cluster-adminsubjects:- kind: ServiceAccountname: admin-usernamespace: kube-system
dashboard-ui.yaml
apiVersion: v1kind: Servicemetadata:name: dashboard-uinamespace: kube-systemspec:selector:k8s-app: kubernetes-dashboardports:- name: webport: 443targetPort: 8443---apiVersion: extensions/v1beta1kind: Ingressmetadata:name: dashboard-uinamespace: kube-systemannotations:kubernetes.io/ingress.class: nginxcertmanager.k8s.io/issuer: "letsencrypt-prod"certmanager.k8s.io/acme-challenge-type: http01ingress.kubernetes.io/ssl-passthrough: "true"nginx.org/ssl-backends: "kubernetes-dashboard"kubernetes.io/ingress.allow-http: "false"nginx.ingress.kubernetes.io/secure-backends: "true"nginx.ingress.kubernetes.io/backend-protocol: "HTTPS"#nginx.ingress.kubernetes.io/whitelist-source-range:spec:tls:- hosts:- <xxxxxx>secretName: <xxxxxx>rules:- host: <xxxxxx>http:paths:- path: /backend:serviceName: kubernetes-dashboardservicePort: 443复制
read-user-sa-rbac.yaml
apiVersion: v1kind: ServiceAccountmetadata:name: dashboard-read-usernamespace: kube-system---apiVersion: rbac.authorization.k8s.io/v1kind: ClusterRoleBindingmetadata:name: dashboard-read-bindingroleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: dashboard-read-clusterrolesubjects:- kind: ServiceAccountname: dashboard-read-usernamespace: kube-system---apiVersion: rbac.authorization.k8s.io/v1kind: ClusterRolemetadata:name: dashboard-read-clusterrolerules:- apiGroups:- ""resources:- configmaps- endpoints- persistentvolumeclaims- pods- replicationcontrollers- replicationcontrollers/scale- serviceaccounts- services- nodes- persistentvolumeclaims- persistentvolumesverbs:- get- list- watch- apiGroups:- ""resources:- bindings- events- limitranges- namespaces/status- pods/log- pods/status- replicationcontrollers/status- resourcequotas- resourcequotas/statusverbs:- get- list- watch- apiGroups:- ""resources:- namespacesverbs:- get- list- watch- apiGroups:- appsresources:- daemonsets- deployments- deployments/scale- replicasets- replicasets/scale- statefulsetsverbs:- get- list- watch- apiGroups:- autoscalingresources:- horizontalpodautoscalersverbs:- get- list- watch- apiGroups:- batchresources:- cronjobs- jobsverbs:- get- list- watch- apiGroups:- extensionsresources:- daemonsets- deployments- deployments/scale- ingresses- networkpolicies- replicasets- replicasets/scale- replicationcontrollers/scaleverbs:- get- list- watch- apiGroups:- policyresources:- poddisruptionbudgetsverbs:- get- list- watch- apiGroups:- networking.k8s.ioresources:- networkpoliciesverbs:- get- list- watch- apiGroups:- storage.k8s.ioresources:- storageclasses- volumeattachmentsverbs:- get- list- watch- apiGroups:- rbac.authorization.k8s.ioresources:- clusterrolebindings- clusterroles- roles- rolebindingsverbs:- get- list- watch复制
ui-read-rbac.yaml
kind: ClusterRoleapiVersion: rbac.authorization.k8s.io/v1metadata:name: ui-readrules:- apiGroups:- ""resources:- services- services/proxyverbs:- get- list- watch---apiVersion: rbac.authorization.k8s.io/v1kind: RoleBindingmetadata:name: ui-read-bindingnamespace: kube-systemroleRef:apiGroup: rbac.authorization.k8s.iokind: ClusterRolename: ui-readsubjects:- apiGroup: rbac.authorization.k8s.iokind: Username: readonly复制
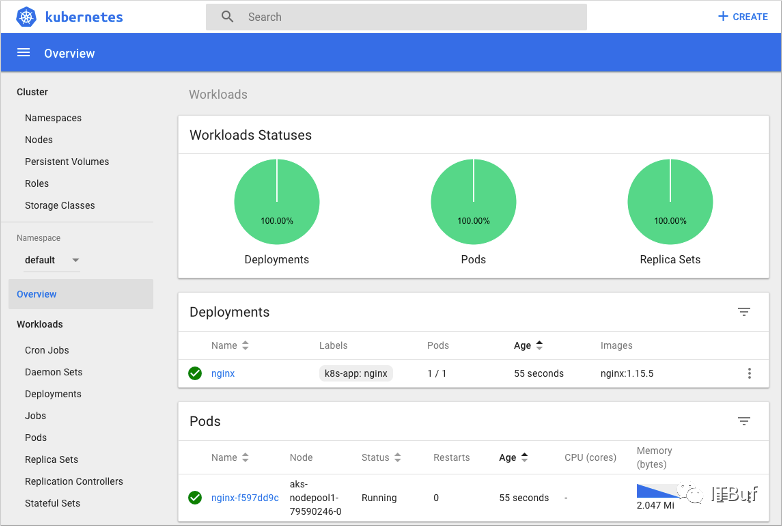
部署
以上总共6个YAML文件,放在同一个目录中应用即可
kubectl apply -f .复制
如果不想给dashboard配置证书那就直接通过NodePort访问,这里要注意一些,不管证书可不可信,一定要通过443端口访问,否则哪怕是访问到了输入token的页面了,输入了正确的token也不能成功登录的。
获取登录Token
kubectl describe -n kube-system secrets admin-user-token-<这里是一个hash值>复制
这样获取的是admin权限的对dashboard上面的pod、deployment、rc等有删除修改权限,
接下来获取只读权限
kubectl describe -n kube-system secrets dashboard-read-user-token-<这里是一个hash值>复制
文章转载自NFT艺术之家,如果涉嫌侵权,请发送邮件至:contact@modb.pro进行举报,并提供相关证据,一经查实,墨天轮将立刻删除相关内容。
评论
相关阅读
数据库国产化替代深化:DBA的机遇与挑战
代晓磊
1314次阅读
2025-04-27 16:53:22
2025年4月国产数据库中标情况一览:4个千万元级项目,GaussDB与OceanBase大放异彩!
通讯员
794次阅读
2025-04-30 15:24:06
【活动】分享你的压箱底干货文档,三篇解锁进阶奖励!
墨天轮编辑部
535次阅读
2025-04-17 17:02:24
一页概览:Oracle GoldenGate
甲骨文云技术
502次阅读
2025-04-30 12:17:56
GoldenDB数据库v7.2焕新发布,助力全行业数据库平滑替代
GoldenDB分布式数据库
481次阅读
2025-04-30 12:17:50
优炫数据库成功入围新疆维吾尔自治区行政事业单位数据库2025年框架协议采购!
优炫软件
369次阅读
2025-04-18 10:01:22
给准备学习国产数据库的朋友几点建议
白鳝的洞穴
351次阅读
2025-05-07 10:06:14
XCOPS广州站:从开源自研之争到AI驱动的下一代数据库架构探索
韩锋频道
316次阅读
2025-04-29 10:35:54
MySQL 30 周年庆!MySQL 8.4 认证免费考!这次是认真的。。。
数据库运维之道
296次阅读
2025-04-28 11:01:25
国产数据库图谱又上新|82篇精选内容全览达梦数据库
墨天轮编辑部
285次阅读
2025-04-23 12:04:21






